I. Why the Traditional Security Model is Broken
Autonomous agents violate the core assumptions of traditional security architecture, creating a massive risk exposure:- The Identity Explosion: Agents are being deployed at an exponential rate, often existing for seconds or minutes (ephemeral lifespans) to complete a single task. This creates identity sprawl where security teams must manage tens of thousands of machine identities that are constantly being created and destroyed, a scale traditional systems cannot handle.
- Indeterministic Behavior: Unlike conventional software with fixed execution paths, AI agents dynamically plan their steps. The same agent performing a routine task can suddenly attempt to access financial data if it believes that action is necessary to achieve its goal. This unpredictability leads to massive privilege escalation risks.
- The Delegation Blind Spot: Agents often act “on behalf of” a human user (delegated authority). Without clear tracking, the audit trail is broken, making it impossible to answer: Which agent executed this action, and who explicitly authorized the agent to do it?
II. The Solution: Dynamic, Purpose-Based Authorization
Securing the autonomous enterprise requires shifting from static, role-based access (RBAC) to dynamic, purpose-based identity management (AIM). . This model centers around four principles:- Unique Agent Identity (AIM): Every agent must be treated as a unique, traceable digital entity with cryptographically bound, short-lived credentials (like OAuth and PKCE tokens). They should never share credentials with humans or be hidden behind generic service accounts.
- Zero Standing Privileges (ZSP): Agents must operate with zero access until they request it. Access is granted Just-in-Time (JIT) for the precise duration and scope of the task, then immediately revoked.
- Purpose, Limit, Duration, Scope (PLDS) Authorization: Access control decisions are based on real-time context. The system restricts access based on the agent’s declared Purpose (the task), Limit (how much data), Duration (how long), and Scope (which systems).
- Continuous Monitoring: Governance must monitor agent behavior for anomalies, such as an agent suddenly accessing a system it was not designed for, and use that information to adjust a real-time “trust score” to block risky actions.
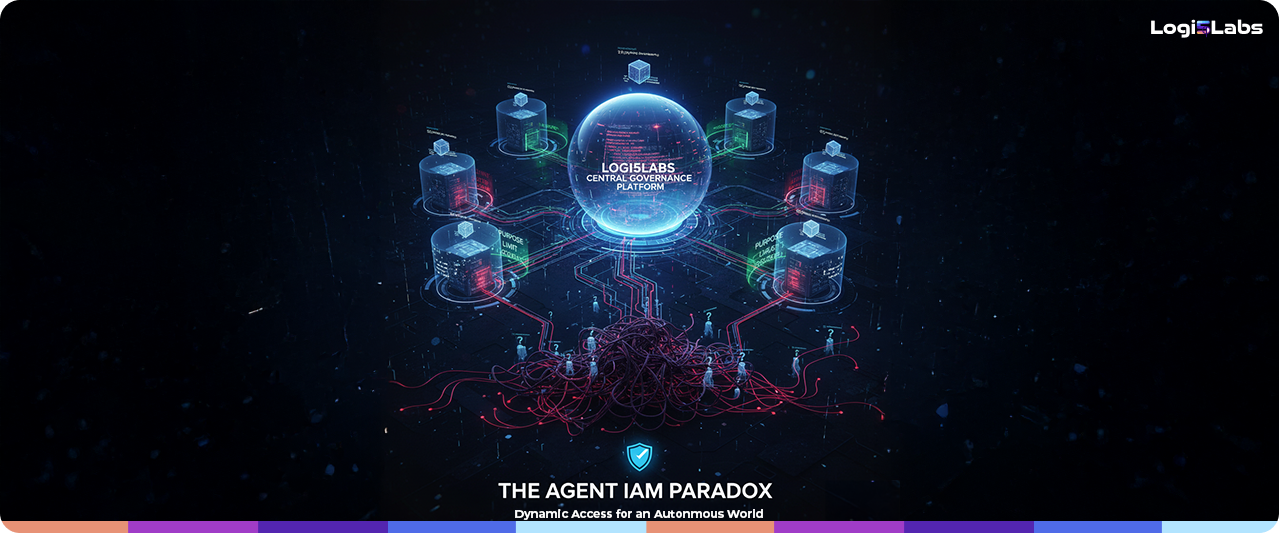
III. Logi5Labs: The Central Access Control Plane for Agents
The Agent IAM Paradox is fundamentally a policy enforcement and orchestration challenge. Traditional IAM systems cannot enforce PLDS policies across dozens of clouds, APIs, and microservices where agents operate. Logi5Labs’ Governance Platform is the Central Identity and Access Control Plane for the Autonomous Agent ecosystem. It provides the essential layer of control:- Enforce Contextual Policy-as-Code: Logi5Labs allows the CISO to define high-level, purpose-based authorization policies (PLDS) and automatically translate them into granular, executable code. This Policy-as-Code engine sits above traditional IAM, ensuring that all access requests are validated against the agent’s declared purpose in real-time.
- Non-Repudiable Auditability: The platform provides the single source of truth for the entire agent lifecycle, recording every action and every decision against the agent’s unique, verifiable identity. This creates the clear, immutable delegation chain necessary for regulatory compliance and forensic investigation.